*************** Thank you for your participation! ***************
| Date: |
12 April 2017 (Wed) |
| Venue: |
Rm 121, Ho Sin Hang Engineering
Building (SHB), The Chinese University of Hong Kong (map here) |
Talk Title & Abstract
Deniable/Covert/Stealthy/LPD Communication |
by Prof. Sidharth JAGGI |
The urge to communicate, to speak and be heard, is a fundamental human need. However, embedded within our increasingly sophisticated communication networks, Big Brother is often watching. There are situations where even the fact that communication is happening (not just the content of that communication), can have real-world consequences. For instance, if you are a politically active citizen in an authoritarian society with broad censorship powers, the mere fact that you are communicating with the outside world can be construed by those authorities as sufficient justification for reprisals.
There has been a flurry of recent work in the information theory community dealing with this problem. In general, this problem encompasses models of communication with dual goals. Firstly, all communication from the source (Alice) to the destination (Bob) should be reliable, i.e., the communication protocol should be resilient to random noise, and perhaps even active jamming. Secondly, if the communication is overheard by a third party (Eve), it should be deniable from Eve. That is, not only should Eve should not learn anything about the source’s message, in fact Eve should not even be able to reliably decide whether or not the source is indeed communicating to Bob. To be able to instantiate such deniability in communication, there need to be asymmetries that might exist between Bob and Eve (for instance, perhaps the noise on the channel to Eve is higher than the noise on the channel to Bob, or perhaps Eve observes only a subset of the transmissions that Bob does).
The tools used are typically information-theoretic and/or coding-theoretic in nature. Typically, deniability is formally defined in terms of a hypothesis-testing metric, and then one demands that the communication protocol that is reliable to Bob also have “high deniability”, regardless of Eve’s estimation strategy. Recently, in various communication settings (wired, wireless and quantum channels/networks), fundamental bounds on optimal rates for deniable communication, and also complementary schemes that are close to optimal.
|
Permutation Capacity of Infinite Graphs |
by Prof. János KÖRNER |

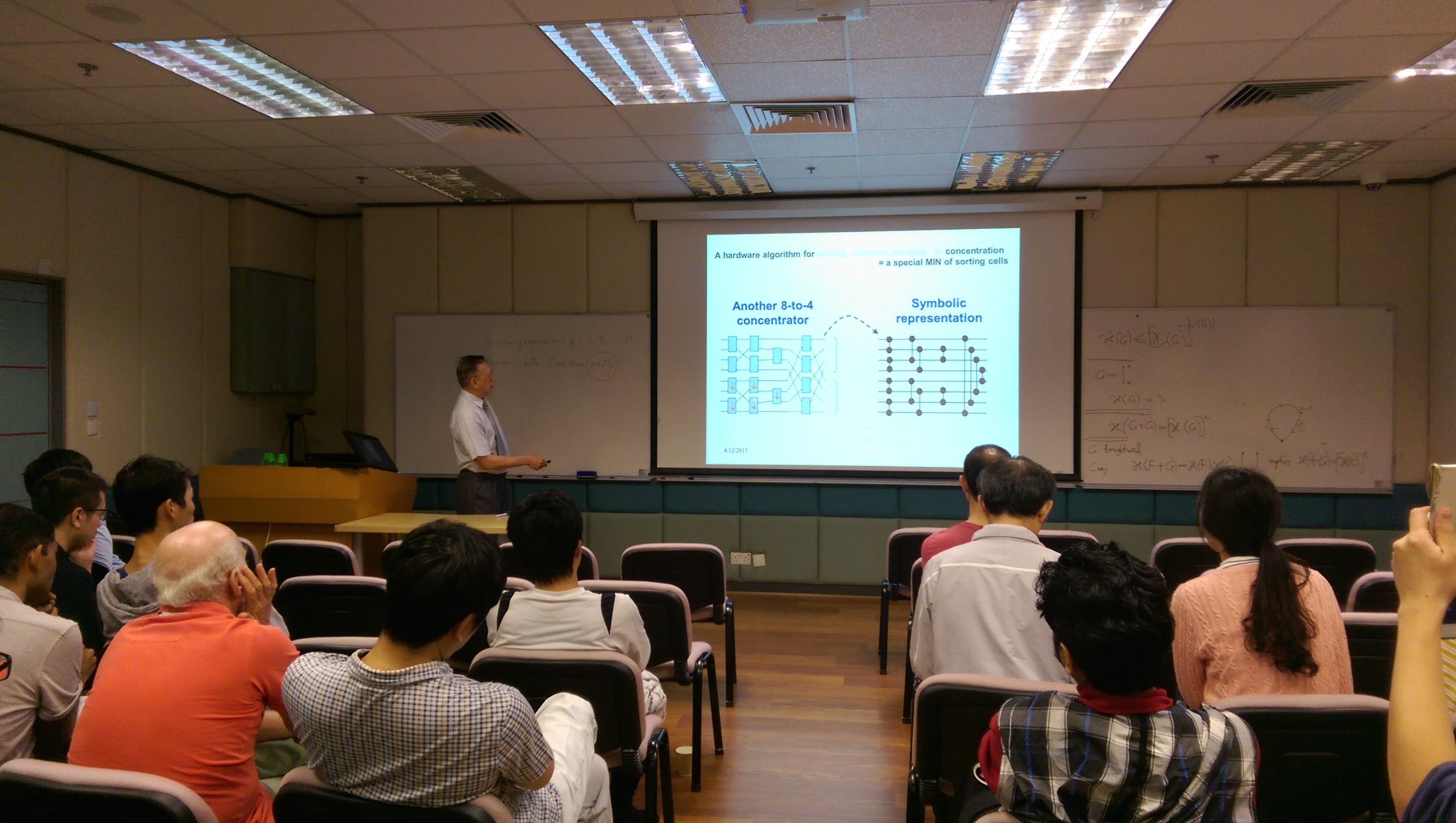
A Connection between Sorting/Routing/Switching Networks and Lattice Theory |
by Prof. Shuo-Yen Robert LI |
On Continuous-Time Gaussian Channels |
by Prof. Guangyue HAN |
| We establish natural connections between continuous-time Gaussian feedback/memorychannels with their associated discrete-time versions in the forms of sampling and approximating theorems. It turns out that these connections, together with relevant tools from stochastic calculus, can enhance our understanding of continuous-time Gaussian channels in terms of giving alternative interpretations to some long held “folklores”, recovering known results from new perspectives, and obtaining new results inspired by the insights and ideas that come along with the connections. In particular, we derive the capacity regions of a continuous-time white Gaussian multiple access channel, a continuous-time white Gaussian interference channel, and a continuous-time white Gaussian broadcast channel; furthermore, applying the sampling and approximating theorems and the ideas and techniques in their proofs, we analyze how feedback affects the capacity regions of families of continuous-time multi-user one-hop Gaussian channels: feedback will increase the capacity regions of some continuous-time white Gaussian broadcast and interference channels, while it will not increase capacity regions of continuous-time white Gaussian multiple access channels.
|

Proving Properties of Error-correcting Codes and Statistical Physics Models via Factor-graph Duality and Ideas from Topology |
| by Prof. Pascal VONTOBEL |

*************** ALL ARE WELCOME ***************